See here for a collection of posts about mental illness diagnosis and how people in political power abuse it.
Exposing Intelligence Agency Human Rights Abuses, Government and Corporate Corruption Along with the Problems of Zionism. The Foundation of Freedom is Freedom of Thought and Freedom of Speech
Friday, September 27, 2024
Saturday, September 21, 2024
An Interesting Video About Smearing Political Enemies- This is What Zionists Love to Do - WWW Internet = 666 In Hebrew - Connected to Finding Political Dissidents
First off, go here to read the Wikipedia entry on COINTELPRO. In addition to watching the video below, you absolutely MUST see the articles below the video. Also, see here, is Zionism/Jewish nationalism apolitical cult?
in Canada from Ritual Defamation
1. Torture, Discrediting With Slander and Organized Stalking
2. Examples Of Counter Intelligence Phonies Who Know About Stasi Organized Stalking & Classified Technology And Keep Quiet About It
3. Zersetzung: The Origins of Modern Day Homeland Security and the Police State
4. Zersetzung: The Origins of Modern Day Homeland Security and the Police State Part 2
5. Zersetzung Part 3 - The New Homeland Security
6. Homeland Security - Organized Stalking and Militant Zionism
7. How to Discredit Someone With Hi-Technology
8. How Covert Agents Infiltrate To Manipulate, Deceive, And Destroy Reputations
9. Front Groups and Intelligence Agents
10. Learning About the Origins of "Homeland Security"
11. Download STASI book
12. Noam Chomsky on COINTELPRO
13. A Perfect Example of a Cointelpro Website
14. Phony Cointelpro Front Websites and the Liars That are Behind Them
15. COINTELPRO and the Phoenix Program
16. COINTELPRO Part 2
17. Gaslighting: What Intelligence and Informant Stalkers Participate In
18. Video Example of Stasi "Anchoring" Techniques
19. How Easy is it to Get People to Engage in Organized Stalking? A Perfect Example of The Naivete of the Public and Putting Too Much Trust in Authority Figures
20. 'Couple Harassed with Organized Stalking Noise Harassment Campaign'
21. Homeland Security Made in Israel
22. Homeland Security is Connected to Zionism
23. Homeland Security: The Strong Connections Between Israel, Canada and the United States
24. CSIS and the RCMP dealing with Political People
25. FBI Infragard and Private Outsourced Intelligence Agents
26. InfraGard: An Unhealthy Government Alliance
27. Proof FBI Snitching & Organized Stalking Program
28. The Current FBI, NSA, CIA, RCMP, CSE, CSIS, and the Canadian Human Rights Commission Leadership That Should Be Prosecuted & Thrown In Jail
Monday, September 16, 2024
Watch the Videos Below, How Many of You People.... Religious Or Not, Are Just Phony Satanists Covering Up This Classified Technology?
Freemasonry Cannot Be Separated From Israel and the Jewish State
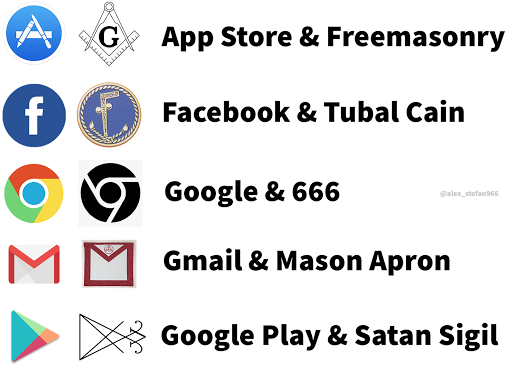
How many of you are a part of this? You can see Masonic symbolism on everything from intelligence agencies, police, government institutions, corporations, Hollywood, Silicon Valley, technology and computer companies, big oil companies, military contractors and the military. See here for is Zionism/Jewish nationalism a political cult?
As far as Jesus Christ goes, to me that is not totally important, (if you don't care,) what is important is showing that these people run the world and they are Freemasons. But ask yourself something... who puts all of the bizarre esoteric information in their movies, (Jews,) and who has the only Masonic symbol on their flag? (Israel.) Six lines, six triangles and six corners = 666. The only flag in the world. Remember, Israel is a Jewish state and on a map it is the center of the earth. So why does it all connect to Israel and Jews? Does it have something to do with Jesus?
One mistake I noticed in the first video... he claims one picture is Aleister Crowley when he was younger when in fact it is Nietzsche. Besides that I think it is pretty good. Not all of the individuals that are a part of Freemasonry even go through these rituals, they are just brought in. This has made it easier for more people to be a part of this.
the oldest intelligence agency
Monday, August 12, 2024
Thursday, August 8, 2024
Targeted Individual Program is US Special Operations Command’s “Continuous Clandestine Tagging, Tracking, and Locating Hostile Forces
Click on Links Below to Read the
Government Documents
The following seven power point presentations made by and for US Special Operations Command (USSOCOM) and their military and corporate partners clearly describe and detail the “technology,” systems, and personnel behind the “organized stalking-electronic torture program."
These power point presentations indicate that this new form of unconventional warfare/low intensity conflict being covertly waged against civilians placed on the Terrorism Watch List under the pretext of the so-called “War on Terrorism” is actually “multi-domain warfare.”
The following terms and technologies, depicted in these power point presentations, strongly suggest that so-called “Clandestine Tagging, Tracking, and Locating (CTTL)”, later termed “Hostile Forces- Tagging, Tracking, and Locating (HF-TTL), is the USAP (Unacknowledged Special Access Project) commonly referred to as the Targeted Individual Program/Organized Stalking-Electronic Harassment.
Furthermore, TIs are obviously the expendable guinea pigs/test subjects for development of these technologies:
2) Technologies include:
Nanotechnology (including Quantum Dot and Self-assembled Photonic Antenna)
Biotechnology (including “biomimetic devices for detection and identification at long distances” and “Taggants for Biological Signature Amplification, Translation,”)
Chemistry (including “signature enhancing Taggants” and “chemical/biochemical sensors for natural signatures”)
3) Participating agencies include: DARPA, Army Research Lab, NSA, DIA, CIA, Homeland Security, FBI, Air Force Research Lab, DOE, and Industry
4) Human signature detection via skin spectral emissivity's, thermal fingerprints at long distance
5) fieldable “bio-electronics”
6) bio-engineered signature translation and bio-reactive taggant (implant)
7) self-assembled photonic antennae
8) biometrics and tactical site exploitation (forensics)
9) Operation “Silent Dagger”
10) Ground SIGINT (Signals Intelligence) Kit (GSK)
11) Joint Threat Warning Systems from the Air, Land, and Sea
12) RF (radio-frequency) and non-traditional (eg., optical/multi-band) Tags and R/Xs
13) “synchronize acquisition of signals intelligence (SIGINT) capabilities across the air, ground and maritime (warfare) domains”
14) SPECIAL RECONNAISSANCE, SURVEILLANCE, AND EXPLOITATION
15) Blue Force Tracking (BFT)
16) Special Operations Tactical Video Systems (SOTVS)
17) Sensitive Site Exploitation (SSE)
18) tiny satellites that keep tabs on targets from above (SpaceX rocket carrying the CubeSats—inexpensive satellites so small they can fit in the palm of your hand)
19) tracking satellites are part of the growing Special Operations focus on “high-value target” missions
20) tracking tags on enemies including radio frequency identification devices, quantum dots that could be used to track a singe molecule, and tagging measures such as insect pheromones
These programs are funded via American tax dollars and deploy regular and irregular (citizen-based agents) forces as well as special forces against innocent citizens.
I. US Special Operations Command: Continuous Clandestine Tagging, Tracking, and Locating (CTTL)
by Doug Richardson SOAL-T WSO, Sept. 5, 2007
Mr. Doug Richardson SOAL-T WSO 5 September 2007. The overall classification of this briefing is: UNCLASSIFIED and Locating (CTTL) The Ability to Locate, Track, and Identify Human Beings.
Highlights From PPT:
p. 3: Continuous Clandestine Tagging, Tracking, and Locating (CTTL)
– The Ability to Locate, Track, and Identify Human Beings and Other Important Targets
- Directly Supports DoD’s Ability to Prosecute the Global War on Terrorism (GWOT)
- Forces Require an Ability to Apply and Monitor Tags
- Detect and Identify Targets Based on Their Unique Observable Characteristics Without Undue Exposure of Personnel to Risks and With Devices That are Sufficiently Clandestine to be Effective.
p. 4: Partnership between Assistant Secretary of Defense for Special Operations and Low Intensity Conflict (ASD SO/LIC), USSOCOM, and U.S. Army
- Objective: Conduct a Collaborative Effort to Develop New Capabilities for Clandestine Tagging, Tracking, and Locating in Response to Priorities Established in a Quick-look Capability-based Assessment Conducted in Response to the Findings of the QDR
- Approach: Transition Existing State-of-the-Art Technologies in Nanotechnology, Chemistry, and Biology to Operational Systems Through the USSOCOM Acquisition Process and Conduct RDT&E From Basic Research Through Prototyping to Provide Continuous Improvements in the CTTL Technology Available for Transition to the Operators. Specific Capability Projections Are Classified.
p. 7: CTTL– Key Enabling Technologies
- Nanotechnology
Clandestine Devices
High Functional-density Devices
Self-organizing, Self-deploying Devices
Processing and Communications
Energy Harvesting
- Biotechnology
Biomimetic Devices for Detection and Identification (ID) at Long Distance Bio-based Devices for Detection and ID at Long Distance Taggants for Biological Signature Amplification, Translation Natural Signature Detection and ID
- Chemistry
Signature Enhancing Taggants
Chemical/Biochemical Sensors for Natural Signatures
p. 8: CTTL– Partnership for Transition–
- DDR&E and USSOCOM AE Executive Sponsorship and Oversight
- USSOCOM Transition
PEO-Special Projects
PEO-Intelligence and Information Systems
- Collaborative Execution of S&T
DoD Service Laboratories
Defense Advanced Research Projects Agency (DARPA)
ASD(SO/LIC) Coordinated Investments
Intelligence Community Research Organizations
DOE Laboratories
p. 13: CTTL — Human Signature Detection
- Skin Spectral Emissivity's Measured
- Thermal Fingerprints Determined
- “Target” Reacquired 90 Minutes Later
Goal: Verification of Capability and Operational Value Within 2 Years
Human Thermal Fingerprint at Long Distance
p. 14: CTTL –Human Signature Detection —
Goal: Demonstration of Fieldable “Bioelectronics” Within 5 Years
Synthetic Dog’s Nose Sensor
p. 15: CTTL — Signature Amplification/Translation
Bioengineered Signature Translation Bio-reactive Taggant
Goal: Move Basic Research to Advanced Development in 3 Years
Current Capability – Bioengineered Signature Translation
p. 16: CTTL — Nano-scale Devices
Quantum Dots
Goal : Micro-scale in 12 Months, Nano-scale in 4 to 5 Years
Self-assembled Photonic Antenna
Sunday, August 4, 2024
All the Laws That Are Currently Being Violated in Canada and Internationally From the Crimes Mentioned On This Blog
See here for how I contacted Prime Minister Justin Trudeau with no reply. See here for how I contacted Head of Public Safety Canada Marco Mendicino and received no reply.
-Violation of the Charter of Rights and Freedoms of Canada
- Violation of the Bill of Rights of Canada
Criminal Code of Canada
- Possession of weapon for dangerous purpose
- Drug Trafficking (many of my stalkers are involved in drugs, probably some of the police and intelligence agents too)
- Human Trafficking (look up the definition of human trafficking)
-Criminal Harassment
- Torture
- Illegal Surveillance
- Espionage
International Law
- Violation of the Geneva Conventions of human experimentation and torture
- Nuremberg Laws and Code on human experimentation and torture
UN Treaties
- International Covenant on Civil and Political Rights
- Convention against torture and other cruel and inhuman or degrading treatment or punishment
- Universal Declaration of Human Rights
Monday, July 22, 2024
Wednesday, July 10, 2024
We are Hackable Animals
There you go. No more rights. Here is the wikipedia of the guy that is featured in the top video below. In the bottom video is Sergey Brin, the co-founder of Google along with Klaus Schwab, the founder of the World Economic Forum. Have you ever seen the movie the Circle, which is loosely based upon Google? Remember the Google Chrome circle? Do you remember in the movie how they were following the guy around? This is organized stalking!
The guy in the top video is Dr Yuval Noah Harari, see interviews with him here, here, and here with James Altucher. I have written previously about James Altucher here, here, and here, The video proves what I am saying. James is a computer scientist, Yuval isn't, but he knows about this. (It is worth mentioning, James is not the only one covering this up.)